Conditional access and data security requirements?
We know that enterprises need to secure their data while keeping productivity in mind.
We were recently engaged in a project that is like many projects we do, a migration from Exchange to Office 365. However, this project was quite different as well.
Unlike most of our Office 365 migration projects, this client had some very specific security and access requirements. With their existing environment, users had no external access to email except through VPN (very limited number of users) or mobile for selected users. OWA, MAPI, etc. was blocked with firewall rules. ActiveSync was only enabled for approved users but there was nothing else in place limiting them from connecting with multiple ActiveSync devices.
With this migration, they had the following desires:
- Give the users the ability to access their email externally without being able to download/dump large amounts of email
- Give users with approved devices the ability to access email using Outlook clients without the need for a VPN
- Secure access to their email by using MFA with the MS Authenticator app
- Continue to use AirWatch for mobile phones and tablets, but use Intune for company laptops
Finding a balance of user acceptance, deployment ease, and securing the data was a challenging but exciting exercise. We were able to meet and exceed their needs using Microsoft Azure AD, Conditional Access, and Intune with Microsoft EMS licensing.
Based on their technical desires we were able to put together this simple table:
| Where | What | Factor(s) | Details |
| Internal Network | Approved device | Username and Password | User has access to use OWA, Outlook client |
| Internal Network | Non-approved device | N/A | Device does not have access to the internal network |
| External Network | Approved device | Username and Password and
Intune or Azure AD Hybrid |
User has access to OWA, Outlook client
Conditional Access checks for compliance (Intune or AzureAD Hybrid) |
| External Network | Non-approved device | Username and Password and
OTP Passcode (Azure MFA) |
Azure MFA is required to provide a OTP passcode. After authentication, ADFS analyzes the claim and if it is from anything other than a web client, it is rejected. |
To achieve this, we needed to control the access at the authentication level. A combination of ADFS and Azure AD Conditional Access was required in this scenario. All authentication requests to O365 start at the ADFS server.
On the ADFS server we configured claims rules that would validate where the request is coming from. If it is an internal request, the ADFS server only requires a Username and password and then accepts the claim. If the request is external, ADFS still accepts the claim with successful authentication, but then sends the request to Azure MFA (Conditional Access).
So great, all we needed to do is make sure our trusted devices are registered as Hybrid Azure AD devices and we are good to go, right? Well, in this case we also had MacOS devices. As of now, MacOS devices cannot be Hybrid Azure AD joined.
Damn.
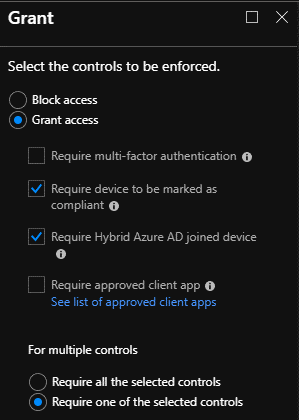
This is what brought on their desire to use Intune for MDM on all approved company laptops. We needed to configure it for the MacOS devices, so we might as well utilize it for Windows 10 laptops as well, as the deployment is very straight for those devices, especially after the back end is configured. As you can see below, using conditional access you can grant access with certain requirements:
For mobile devices, we had to bypass conditional access. This is because the setting “Require device to be marked as compliant,” only works with Intune. Since we are using AirWatch for mobile devices and we wanted to control which devices had ActiveSync access, we had to bypass conditional access. Note, we couldn’t use the “Require approved client app,” setting because they wanted to use the native mail client for iPhone users. So, for mobile devices we decided to use Exchange Online mobile access control to quarantine all ActiveSync devices and only allowed approved devices to access email. Unfortunately, we couldn’t just import all device ID’s and allow them because we wanted to use Outlook mobile for Android devices, which creates an ID when you install it. This would be new for Android users migrated to the cloud instead of using their native mail client. Yes, this is a little more work for the admins, but that is part of the security/functionality balance that we all know so well.
So, we configured Hybrid Azure AD, Intune, and Exchange Online mobile access policies. Using those combined with ADFS and Conditional Access, we were able to create very granular access scenarios that meet security requirements without being too complex for the admins and end users.
With the continuous release of new technology, we are seeing that conditional access is something that should always be implemented. How many enterprises have you been to that have either way too strict access policies, or a way too lax/nonexistent policies (turn a blind eye, everyone has access) when it comes to data in the cloud? We can configure environments to allow seamless user access to data while maintaining security and control over the data.
Here at iRangers, we are always finding the best ways to help enterprises secure their data while keeping in mind the people that need to use the technology and still be productive. If data security and conditional access is something you need, contact us.