“WannaCry, Wcry, and WannaCrypt enter the bank… Hands up! It’s a robbery – shouts one of them! Give us all your money (or just $300 bucks) for a password and no file will be hurt.”
Friday morning was a sunny morning without any sign of the approaching storm. By virtue of being up here in Canada, a lot happens in business hours around the world while we’re sleeping but conversely, that’s given us some time to collate information whilst everyone else is taking a break.
The WannaCry incident is both new and scary in some ways and more of the same old stuff in others. Here’s what I know and what the masses out there need to understand about this and indeed about ransomware in general.
Meet the Ransomware family
Let’s begin with a short history lesson. The first signs of ransom virus were seen around 1999 and one of them was called “The AIDS trojan”. You can read more about it here.

Fortunately for the mankind, the technology those days was undeveloped enough to spread the virus and it was distributed via floppy disk to the (comparatively) a small number of people who had PCs and requested that they send (via snail mail) a cashier’s cheque or money order.
Fast forward to the modern era and we have billions of people using the world’s largest malware distribution network (we also call this “the internet”) and Bitcoin as the currency of choice for ransoms. So, whilst ransomware has been around for ages, it’s only seriously gained traction in more recent times.
Most of the modern ransomware variants encrypt personal files on an infected machine. The first people usually know of an infection is that files aren’t readable or they’re faced with a ransom notice.
The situation with WannaCry / Wcry / WannaCrypt
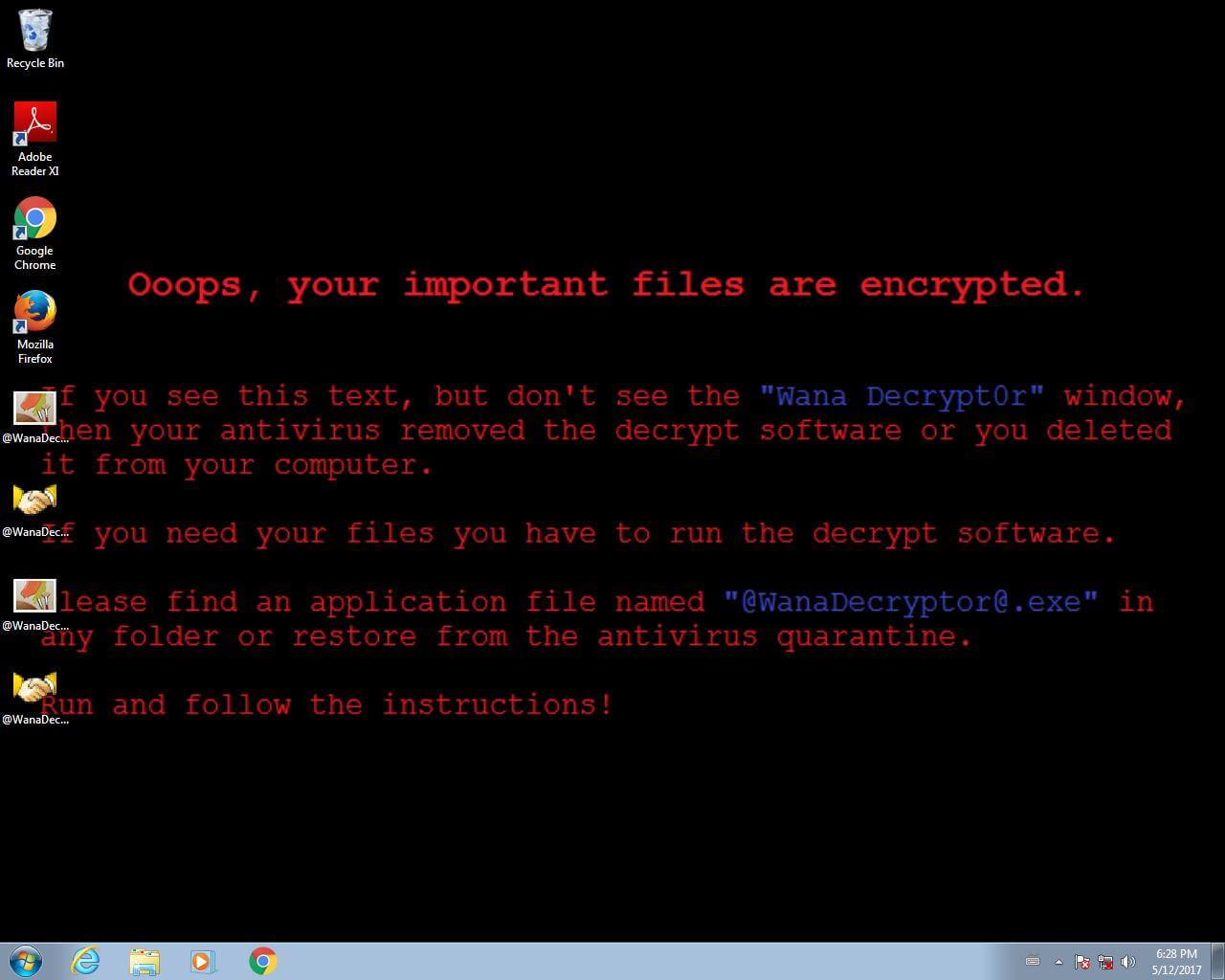
Let’s cover the fundamentals here, starting with the ransom demand shown on infected machines
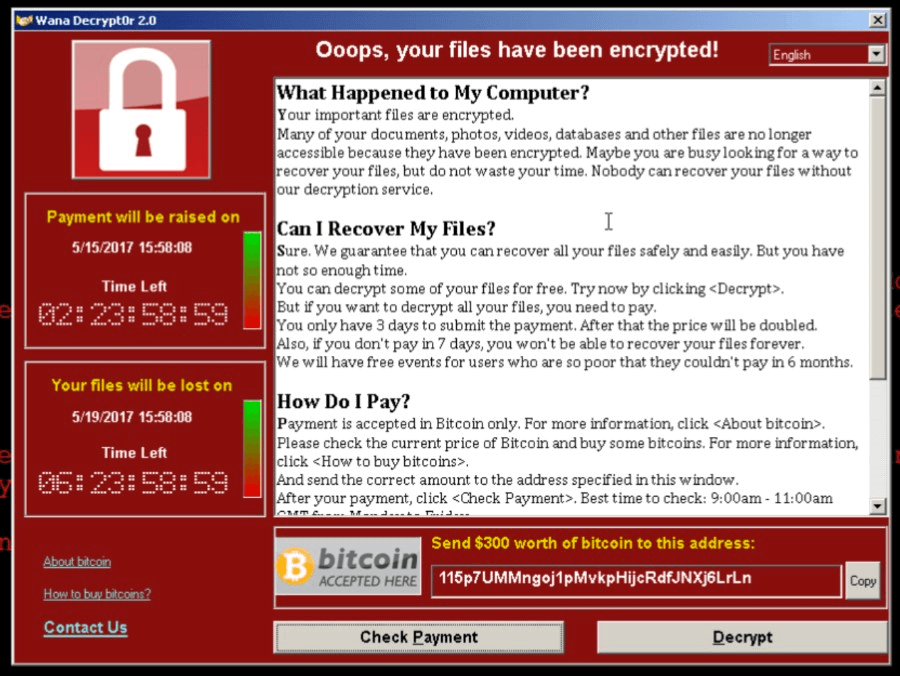
The ransom is $300 and you’ve got 3 days to pay before it doubles to $600. If you don’t pay within a week then the ransomware threatens to delete the files altogether. Note the social engineering aspect here too: a sense of urgency is created to prompt people into action. A sense of hope is granted by the ability to decrypt a sample selection of the files. (Note the “Wana Decrypt0r” title on the window above: the three terms WannaCry, Wcry and WannaCrypt are all referring to the same piece of malware, they’re merely various representations of the same name.)
Behind the scenes
The malware spread via SMB, that is the Server Message Block protocol typically used by Windows machines to communicate with file systems over a network. An infected machine would then propagate the infection to other at-risk boxes.
It’s able to do this where the machine supporting the protocol has not received the critical MS-17-010 security patch from Microsoft which was issued on the 14th of March and addresses vulnerabilities in SMBv1 (Microsoft doesn’t mention SMBv2 but Kaspersky has stated that WannaCry targets v2 as has Symantec). In other words, you had to be almost 2 months behind in your patch cycle in order to get hit with this. Windows 10 machines were not subject to the vulnerability this patch addressed and are therefore not at risk of the malware propagating via this vector. Likewise, I’ve seen no commentary suggesting that other SMB implementations such as Samba are impacted.
The ransomware is encrypting basically everything it can get its hands on in terms of connected or networked devices:
The file tasksche.exe checks for disk drives, including network shares and removable storage devices mapped to a letter, such as ‘C:\’, ‘D:\’ etc. The malware then checks for files with a file extension as listed in the appendix and encrypts these using 2048-bit RSA encryption.
The spread of WannaCry has been via SMB so when we’re talking about machines behind firewalls being impacted, it implies ports 139 and 445 being open and at-risk hosts listening to inbound connections. It’d only take one machine behind the firewall to become infected and then put others at risk due to it being self-propagating. Because of the nature of the web and the broad range of unpatched machines, infection rates rapidly spread to tens of thousands of machines across the world:
The first detection of this variant of malware occurred shortly before 9 am UTC on the 12th of May. Analysts also noted that there were requests to iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com beginning at 07:24 which is the first external indicator of compromise. The headline stories which I awoke to in Canada very much focused on the UK’s NHS (their National Health Service) and they were in pretty bad shape. But we’ve subsequently seen reports of all other sorts of organizations around the world being impacted which isn’t at all surprising; ransomware doesn’t tend to discriminate.
The “KILL“ switch
That domain – iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com – is a “randomly” human-typed address which primarily consists of keys in the top row of the keyboard. In other words, someone smashed his head on the keyboard to generate it.
This was found in the WannaCry code:
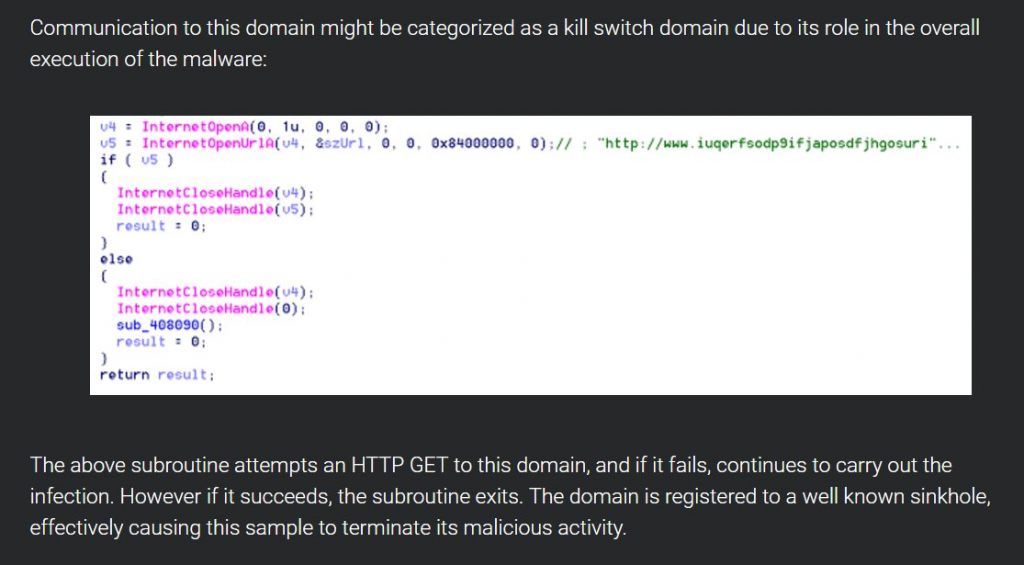 If the malware could communicate with the hostname, it would exit but because that name wasn’t registered, it continued to execute. Well, that is until a researcher worked out what was going on and simply registered the domain name!
If the malware could communicate with the hostname, it would exit but because that name wasn’t registered, it continued to execute. Well, that is until a researcher worked out what was going on and simply registered the domain name!
I’m yet to see a good analysis on why the kill switch existed in the first place and why discovery and circumvention were so simple. It seems entirely counter-intuitive to the goal of infecting as many machines as possible as quickly as possible and I hope we see some good analysis of that soon. The important thing here though is that based on the analysis we’re seeing, this variant shouldn’t be spreading any further, however… there’ll almost certainly be copycats. In fact, that’s enormously important and it also speaks to the futility of virus definition signatures; watch this thing come back with a vengeance after a few modifications. If it was me, I’d be taking any at-risk machine off the wire until it’s patched.
Payments
There are references to 3 different Bitcoin addresses for which we can observe the transactions:
- 13AM4VW2dhxYgXeQepoHkHSQuy6NgaEb94
- 12t9YDPgwueZ9NyMgw519p7AA8isjr6SMw
- 15p7UMMngoj1pMvkpHijcRdfJNXj6LrLn
At the time of writing, there were near $100k ransom fees paid. It’s a nice little earn yet on the other, for tens of thousands of infections to have totaled only 152 payments seems small. That could well go up though; regardless of the kill switch, many machines remain infected and if there’s a 3-day window of payment before the cost escalates, you’d expect plenty of people to be holding off for a bit. It’ll be interesting to look at those Bitcoin addresses in another 48 hours.
It’s because you didn’t upgrade or patch your things
You know how people say you should keep your software up to date, right? Hello? The eternal problem is that for individuals, there’s the often the attitude of “well it works fine, why should I change it?” and this is enormously dangerous. Newer versions of operating systems, for example, typically get a raft of additional defenses. Windows 10 (you know, the version not vulnerable to WannaCry…) got features such as ELAM to protect against malware during the boot cycle. When we look at the problem today hitting machines as old as Windows XP, we’re talking about a 16-year-old operating system that was superseded a decade ago and terminated the support 3 years ago. (Although note that Microsoft has released an out of band patch to protect XP users against WannaCrypt.) And for the less tech-minded, when we say “patch your things”, in this case, it’s nothing more than allowing Windows Update to do precisely what it’s configured to do straight out of the box – just don’t disable it!
And then there’s “The Enterprise”. Organizations are notoriously bad at keeping software modern, especially those in the public sector. Now in their defense, it’s a non-trivial exercise when you’re talking about a large number of machines. Organizations need to be proactive in monitoring for, testing and rolling out these patches. It’s not fun, it costs money and it can still break other dependencies, but the alternative is quite possibly ending up like the NHS or even worse. Bottom line is that it’s an essential part of running a desktop environment in a modern business. Organizations often just simply don’t budget for this stuff and when the CIO eventually comes cap in hand asking for cash, the money isn’t there – “but everything is working ok at the moment, right?”
And it’s worse because you don’t have (proper) backups
One of the most fundamental defenses against ransomware is the ability to reliably restore from backup. If all your things get crypto’d and you can just say “oh well, it’s not fun and I need to rebuild my machine but at least I’ve only lost time” then you’re in a fundamentally better position than having lost your files (short of paying the ransom, that is).
Many (probably most) individuals and organizations alike don’t have a satisfactory backup strategy. Typically, problems include:
- They’re not taking backups at all
- They’re backing up over existing backups and writing corrupted files over good ones
- They’re not backing up frequently enough (it must be fully automated)
- They’re only backing up to connected devices accessible by malicious software
Ideally, you want a 3-2-1 backup strategy which means at least 3 total copies of your data, 2 of which are local but on different mediums (such as external storage devices) and 1 which is offsite. There are professional cloud backup services available which will keep versioned copies of all your things and allow you to rollback to any point in time (no, Dropbox alone won’t do that). There are cheap external devices with large capacities you can physically rotate and store with a trusted relative.
Is this the NSA’s fault?
The SMB vulnerability Microsoft patched was known by the NSA. We know this because the Shadow Brokers leak last month referred to it specifically as “ETERNALBLUE”, an SMBv2 exploit. A month ago, we knew this could be bad news. And sure enough, the vulnerability was quickly exploited which is not at all surprising given the way in which it had now been publicly disclosed. But remember, that’s one month after the vulnerability had already been patched, so what’s the worry?
Well obviously, and as you well know if you’ve read this far, people (and companies) don’t always patch their things. But the political bit was already making headlines in April and it effectively boiled down to arguing that the NSA should be in touch with companies like Microsoft as soon as they discover these risks so they can be patched. On the other hand, the surveillance argument is that these vulnerabilities are enormously useful for intelligence agencies to do precisely what we want them to do which is to gather intelligence on targets (let’s just assume for a moment that they do this responsibly…) Yet still, you can’t ignore the irony of how not just the underlying vulnerability but also the NSA exploit code has impacted the world, including governments themselves:
The thing is though, even with a whole 2 months of lead time we still have this problem of large scale compromise so simply asserting that earlier disclosure and patching would solve the problem isn’t quite accurate. It’s a politically charged debate and frankly, the only thing we can uniformly agree on here is that we’ve got to get better at patching our things.
Where to now?
Well, we’re pretty much in clean-up mode. AV vendors are releasing signatures to identify the malware and we’re all assessing what the total damage will be whilst wait for new variants to follow. But the bigger lessons out of all of this are the ones that reinforce what the security community has been telling people for so long, namely the following:
- Keep your operating systems current
- Take patches early
- Have a robust backup strategy
- Lock down machines
- Don’t open suspicious email or attachments
- Restrict access to network resources (ransomware can only encrypt what it can access or what machines it can propagate to can access)
- Block unnecessary ports (Disable SMB external access)
- Traditional anti-virus is bad at identifying this stuff
All of this is so much more important than WannaCry / Wcry / WannaCrypt and until we get that right, other subsequent variants will hit those who are unprepared. And they’re the real lessons here – not just installing MS-17-010 and being done with it – so until we get those right, this is just one of many more incidents to come, and we see that WannaCry v2.0 is on his way back already.
Right in your email inbox
Useful data from iRangers Experts
Subscribe to our mailing list and get interesting updates and tips.