Recently, our office got an email from somebody who claimed to represent a “Seitz Law Firm” in Miami.
See the email below:
Well, from the first sight, this email looks “Ok,” however, we’ve never had any communication or business with this company.
Then, when you notice the email it was sent from – [me_ceo@aol.com], they had me curious and I wanted to see what the bad guys tried to extract from us.
However, before that, if you will go to the official website of the company, you will see that their domain is: https://seitzlawfirm.com/, and probably their email looks like this: name.lastname@seitzlawfirm.com and definitely not something.stupid@aol.com
Moreover, browsing their website, we discovered that they have only two locations in the US and none of them in Miami.
If you will do a little research, and type the street name from the signature, it will take you nowhere since this number doesn’t exist. However, the neighbourhood looks nice though.
Now, for the email itself. It came with a PDF attachment that you should never, never ever and I mean it, NEVER should you open it if you don’t have a sandboxed environment where you can play with it and manipulate with the malicious files at your free time. In case you missed the part where I say never open attachments if you don’t trust the sender, then… DON’T OPEN IT!!!
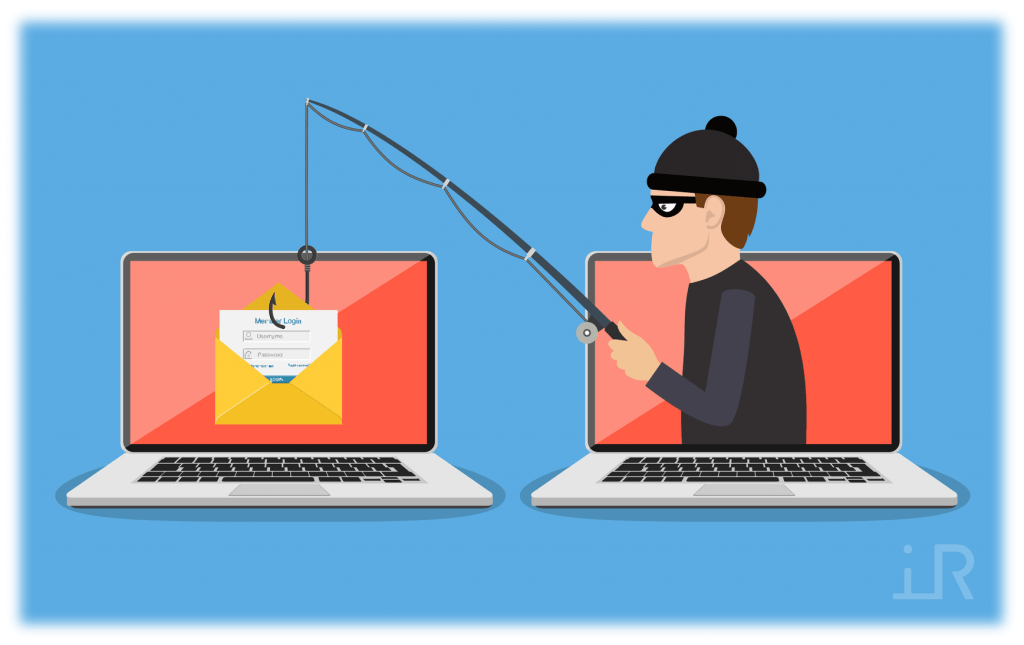
The PDF file looks like this after putting the password in:
General knowledge: Password protected documents are not scanned by mail gateways, antivirus, and any other protection system since they just don’t know how to open that attachment to scan for known viruses, malicious codes, known malicious URL redirects, etc.
How surprising, the PDF didn’t give us any information regarding the “court order” that I was so interested to see and the only option to proceed from here is to click on “View .PDF Online” button in the document. If you came to this point and still have doubts if you should click on it – then don’t! It could be very pricey and painful process of getting your system back. However, I did continue to play with it, and after I clicked on the button, it took me to “legitimate” OneDrive website.
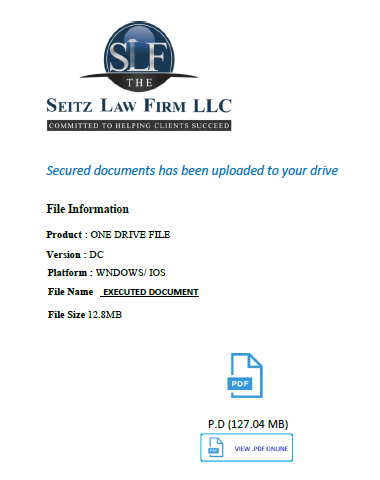
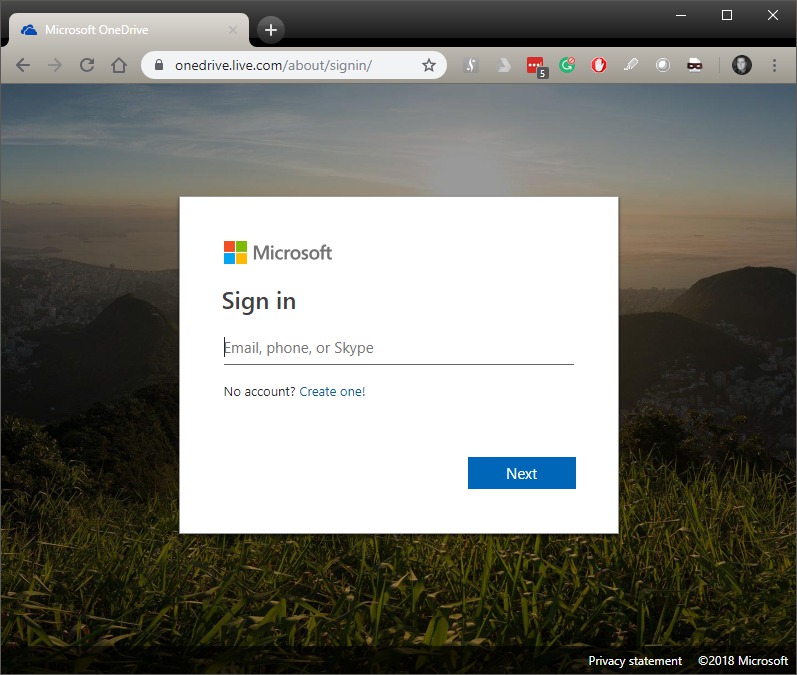
For those who saw a OneDrive website a few times in their life, know that the site looks like this:
But in my case, I got this website: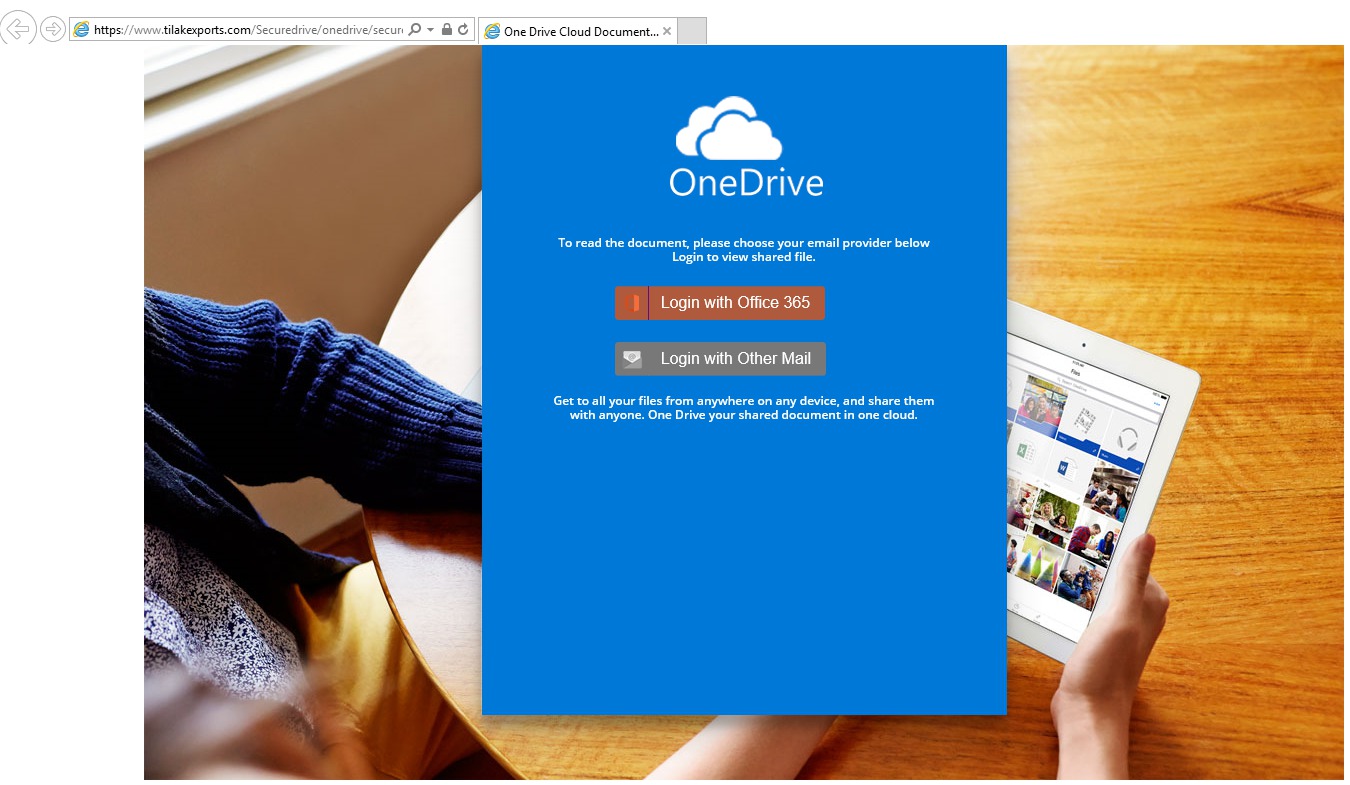
Even if you ignore for a second how this website looks like, check out this crazy URL that they are using:
https://www.tilakexports.com/Securedrive/onedrive/secure/index.php
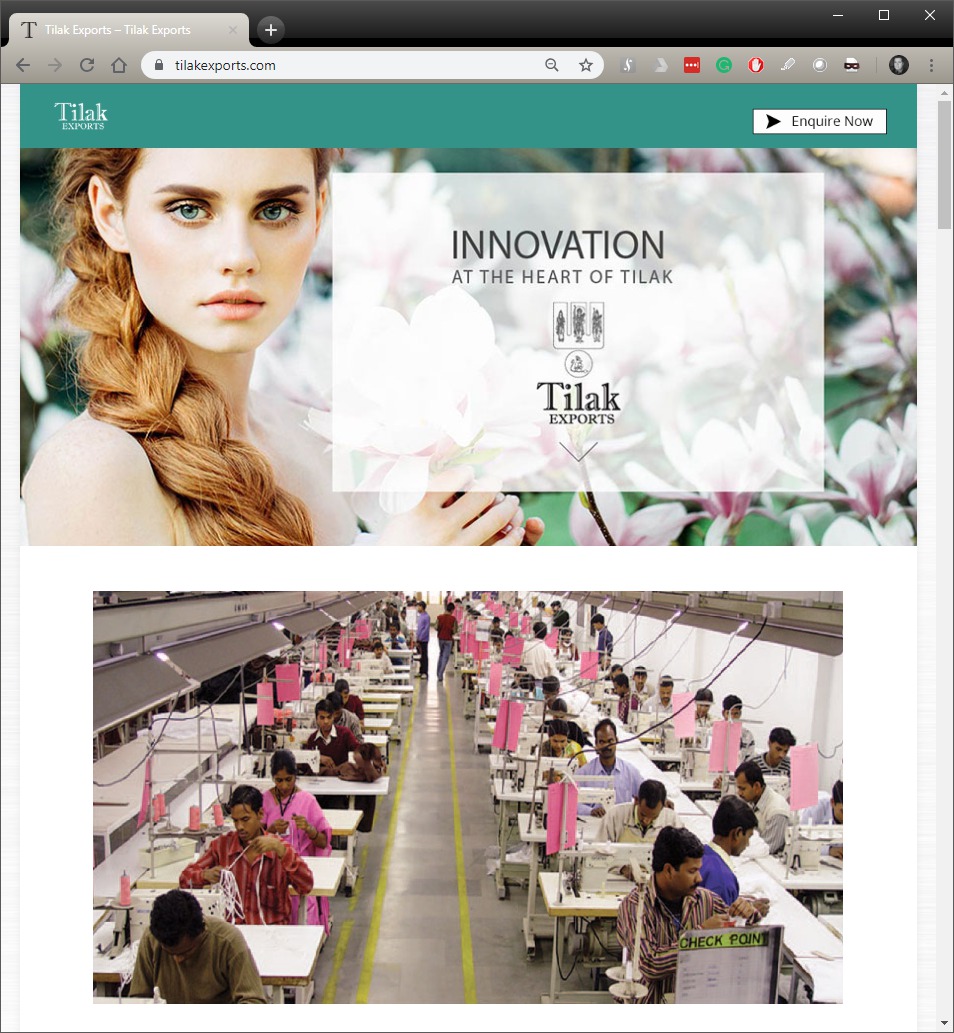
Moreover, this is how their main page looks like:
I am not a website design guru, but I think that a law firm’s site should look a little bit different.
At least from cybersecurity point of view, I am happy that they have Check Point installed in production (lower right corner sign) ?
Now, back to our guest today, the original link.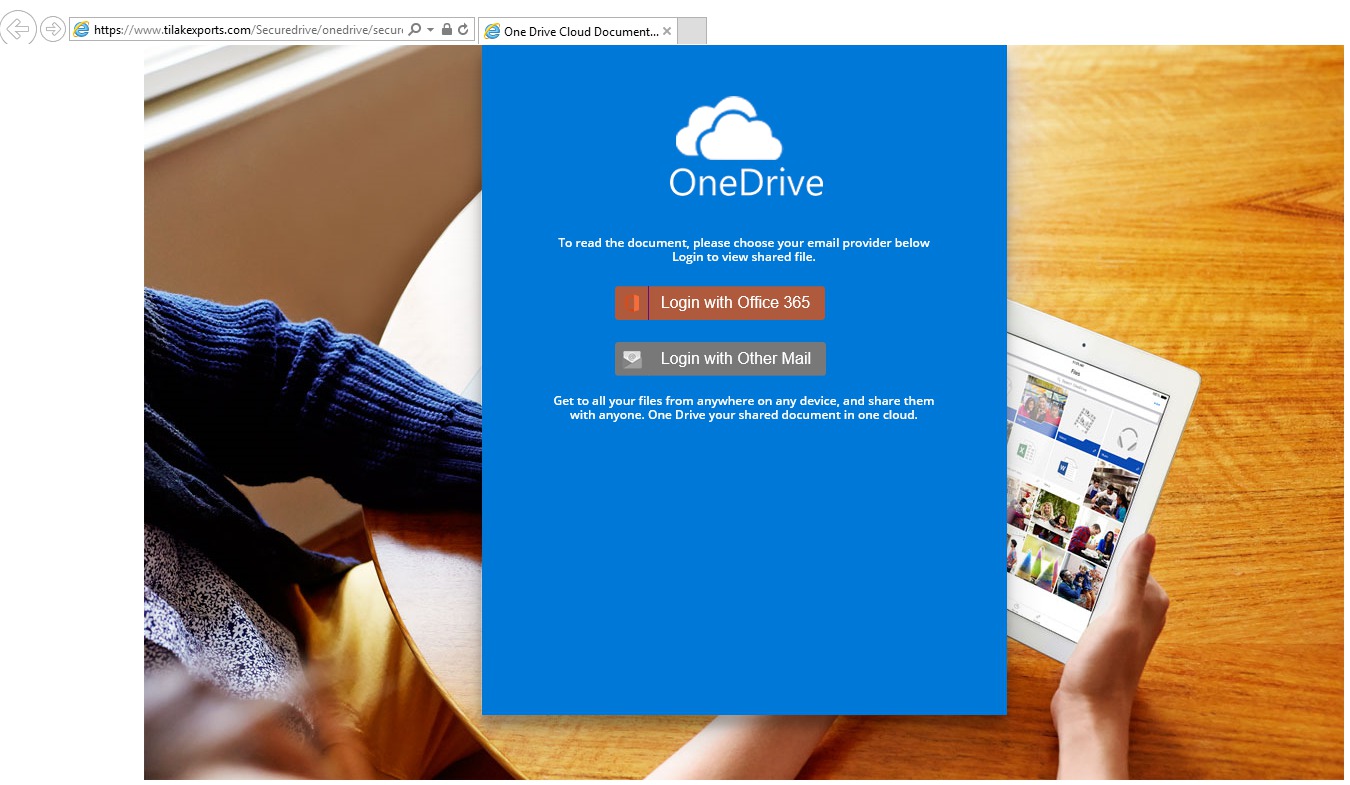
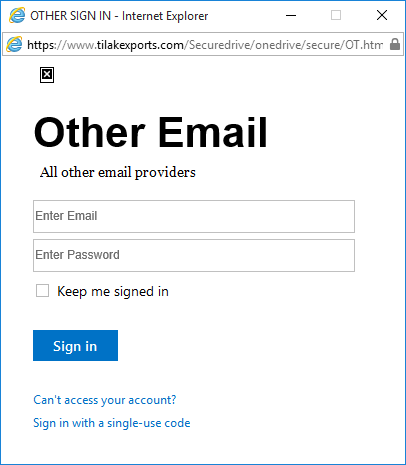
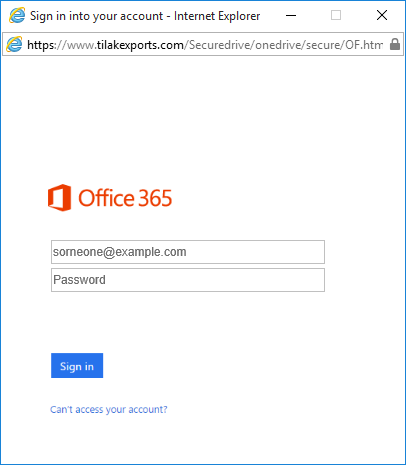
If you click on both “Login” buttons, you will get a different login window accordingly:
These guys didn’t even bother to use pages with links instead of using popup windows with screenshots of the original login screens. So, in case you forgot your password, and you try to “Recover your password” you can’t since the recovery links are the part of the picture and there is no actual link behind it… Amateurs ?
Also, if you’ll note, the links on top of those popups are going to the same “Official” website with the Check Point in production ?
So, to conclude it all, trust me – don’t trust anyone. Well, if it looks fishy, smells fishy then it’s probably fishy or in our case – phishy.
The reason why those people send these emails is to deceive you into putting your credentials and from that moment you will be exposed by letting them inside of your email, cloud storage and other online personal locations.
Interested in how to protect your data from cyber attacks? Learn from iRangers’ cybersecurity experience.
Be safe and don’t be the next victim.
By Dima Zodek